Active Directory Join
In this video, we walk through the process of joining an Active Directory realm. This is important for authentication in Posit Workbench
image: thumbnail.jpg
Transcript#
This transcript was generated automatically and may contain errors.
Hey everyone, my name is Cecil and I'm here with my colleague Jay and we're from the Posit Support team and we're going to show you how to connect your Workbench host to Active Directory.
So connecting to Active Directory is mostly done through the command line and our documentation has most of the steps to do so. There are variations depending on how your Active Directory is configured, but we're going to follow the standard way in our Workbench documentation with connecting Ubuntu 24 to our Active Directory. So we'll start with the first command, which is to install the dependencies.
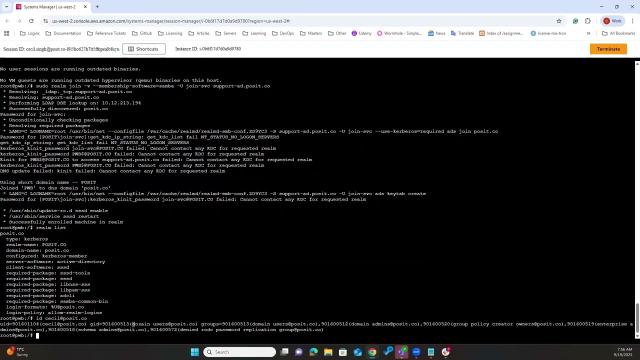
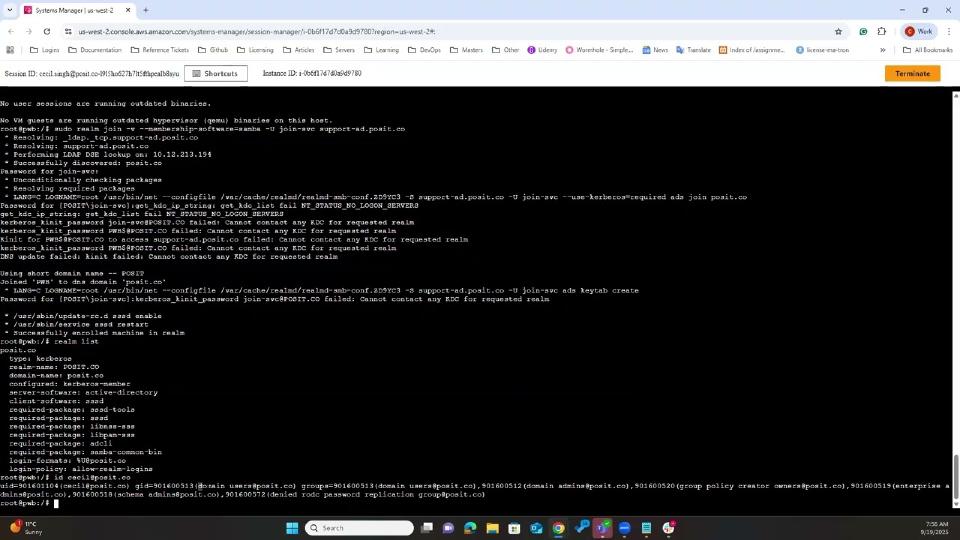
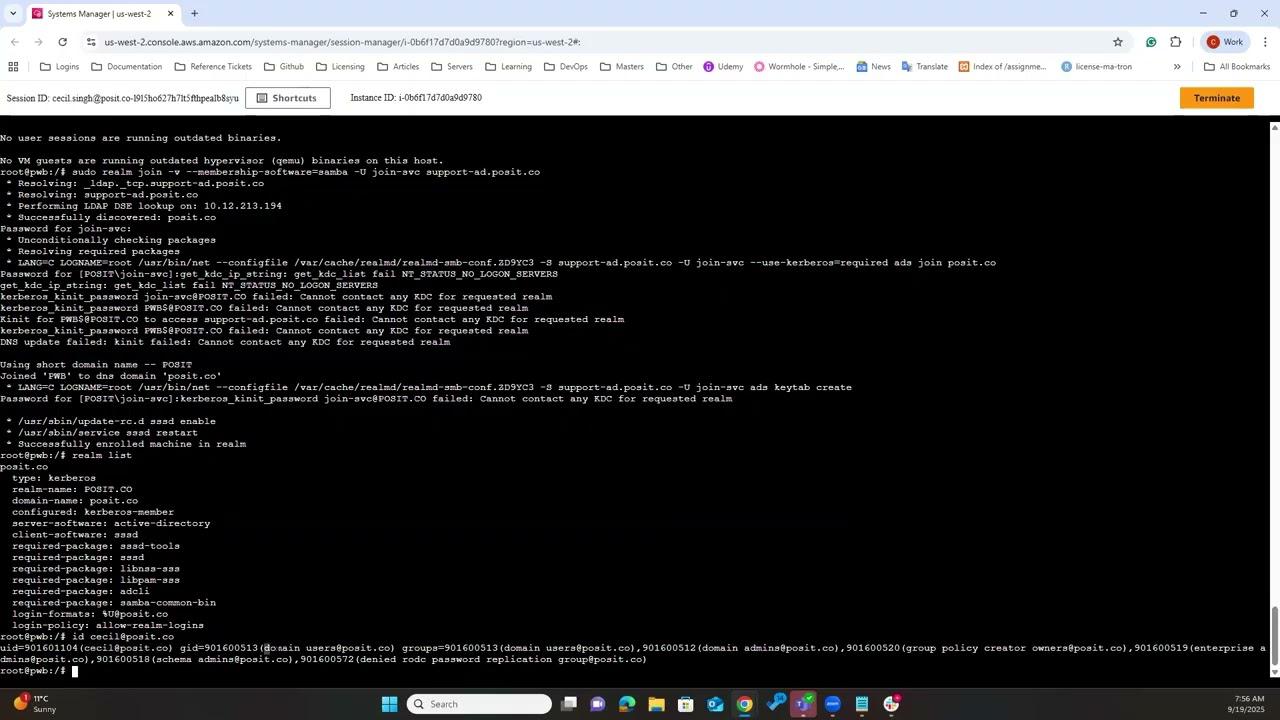
Once that's complete, we can go ahead and join the realm. Something that's a little bit different from the documentation to the command that we're using here is the membership software flag. Because the Active Directory is on the latest version of Windows, Windows 2025, or rather Microsoft Server 2025, it doesn't want to connect unless we have the membership software set as Samba and there are a few open issues about that on Microsoft communities, but we're going to use that command which will prompt us for a password and the password we can enter it in there.
And if that works, you'll see successfully enrolled machine in realm and you can do a realm list just to check that you're enrolled in the correct realm if you have multiple Active Directory hosts. So you can see the realm name there. In this case, it's posit.co. And if you'd like to verify one of your users, you can ID them. And if this works, you know you're connected to the right realm.
So if we ID the user, we can see that this user is and all the groups that they're part of.
Configuring Workbench to use Active Directory
So now that you're connected to the realm, that connects your Linux server to the Active Directory. Now we need to point Workbench to start using your Active Directory credentials. So we can copy the login PAM profile.
And we're going to be using PAM with SSSD today to configure this. So now if we go to we need to open up a file and make an addition to automatically create home directories. You can manually create them as well, but in most cases, creating them automatically is a little bit easier. So that's in the etcpam.d common session file.
And we'll scroll down to session required PAM underscore unix.so. And you can paste this in. This is also mentioned in our official documentation, so you can refer to that if you want to get the exact line.
So once that's done, we can save that.
And one more thing that in most cases you won't need to do, but in for this demo, we don't have any group policies set on the Active Directory. So what we have to do is we have to make an adjustment to our sssd.conf because otherwise we won't be able to log in. We effectively need to set all group policies so that they're not enforced when we try to log in. Otherwise, that will block us. So run this command.
You may not need to run this, but I would suggest consulting your IT team if you would like to, if you need this command or whether you don't.